March/2020 New CCNA 200-301 Exam Dumps with PDF and VCE New Released Today! Following are some new 200-301 Real Exam Questions!
New Question
What is a benefit of using a Cisco Wireless LAN Controller?
A. Central AP management requires more complex configurations
B. Unique SSIDs cannot use the same authentication method
C. It supports autonomous and lightweight APs
D. It eliminates the need to configure each access point individually
Correct Answer: D
New Question
Which network allows devices to communicate without the need to access the Internet?
A. 1729.0.0/16 B. 172.28.0.0/16 C. 192.0.0.0/8
D. 209.165.201.0/24
Correct Answer: B
Explanation:
This question asks about the private ranges of IPv4 addresses. The private ranges of each class of IPv4 are listed below:
Class A private IP address ranges from 10.0.0.0 to 10.255.255.255 Class B private IP address ranges from 172.16.0.0 to 172.31.255.255 Class C private IP address ranges from 192.168.0.0 to 192.168.255.255
Only the network 172.28.0.0/16 belongs to the private IP address (of class B).
New Question
Which result occurs when PortFast is enabled on an interface that is connected to another switch?
A. Spanning tree may fail to detect a switching loop in the network that causes broadcast storms
B. VTP is allowed to propagate VLAN configuration information from switch to switch automatically.
C. Root port choice and spanning tree recalculation are accelerated when a switch link goes down
D. After spanning tree converges PortFast shuts down any port that receives BPDUs.
Correct Answer: A
Explanation:
Enabling the PortFast feature causes a switch or a trunk port to enter the STP forwarding-state immediately or upon a linkup event, thus bypassing the listening and learning states. Note: To enable portfast on a trunk port you need the trunk keyword “spanning-tree portfast trunk“
New Question
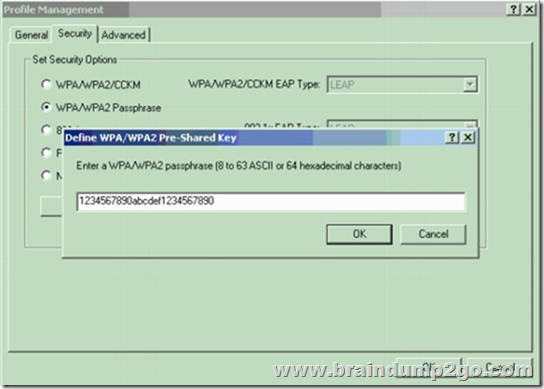
When configuring a WLAN with WPA2 PSK in the Cisco Wireless LAN Controller GUI, which two formats are available to select? (Choose two)
A. ASCII
B. base64
C. binary
D. decimal
E. hexadecimal
Correct Answer: AE
Explanation:
When configuring a WLAN with WPA2 Preshared Key (PSK), we can choose the encryption key format as either ASCII or HEX. Reference: https://www.cisco.com/c/en/us/td/docs/wireless/controller/9800/config-guide/b_wl_16_10_cg/multi-preshared-key.pdf
New Question
Two switches are connected and using Cisco Dynamic Trunking Protocol SW1 is set to Dynamic Desirable What is the result of this configuration?
A. The link is in a downstate.
B. The link is in an error disables state
C. The link is becomes an access port.
D. The link becomes a trunkport.
Correct Answer: D
New Question
When configuring IPv6 on an interface, which two IPv6 multicast groups are joined?(Choose two)
A. 2000::/3 B. 2002::5 C. FC00::/7 D. FF02::1
E. FF02::2
Correct Answer: DE
Explanation:
When an interface is configured with IPv6 address, it automatically joins the all nodes (FF02::1) and solicited-node (FF02::1:FFxx:xxxx) multicast groups. The all-node group is used to communicate with all interfaces on the local link, and the solicited-nodes multicast group is required for link-layer address resolution. Routers also join a third multicast group, the all-routers group (FF02::2).
New Question
Which MAC address is recognized as a VRRP virtual address?
A. 0000.5E00.010a B. 0005.3711.0975 C. 0000.0C07.AC99 D. 0007.C070/AB01
Correct Answer: A
Explanation:
With VRRP, the virtual router’s MAC address is 0000.5E00.01xx , in which xx is the VRRP group.
New Question
in Which way does a spine and-leaf architecture allow for scalability in a network when additional access ports are required?
A. A spine switch and a leaf switch can be added with redundant connections between them
B. A spine switch can be added with at least 40 GB uplinks
C. A leaf switch can be added with a single connection to a core spine switch.
D. A leaf switch can be added with connections to every spine switch
Correct Answer: D
Explanation:
Spine-leaf architecture is typically deployed as two layers: spines (such as an aggregation layer), and leaves (such as an access layer). Spine-leaf topologies provide high-bandwidth, low-latency, nonblocking server-to-server connectivity.
Leaf (aggregation) switches are what provide devices access to the fabric (the network of spine and leaf switches) and are typically deployed at the top of the rack. Generally, devices connect to the leaf switches. Devices can include servers, Layer 4-7 services (firewalls and load balancers), and WAN or Internet routers. Leaf switches do not connect to other leaf switches. In spine-and-leaf architecture, every leaf should connect to every spine in a full mesh.
Spine (aggregation) switches are used to connect to all leaf switches and are typically deployed at the end or middle of the row. Spine switches do not connect to other spine switches. Reference: https://www.cisco.com/c/en/us/products/collateral/switches/nexus-9000-series-switches/guide-c07-733228.html
New Question
Which type of wireless encryption is used for WPA2 in pre-shared key mode?
A. TKIP with RC4
B. RC4
C. AES-128
D. AES-256
Correct Answer: D
Explanation:
We can see in this picture we have to type 64 hexadecimal characters (256 bit) for the WPA2 passphrase so we can deduce the encryption is AES-256, not AES-128.
New Question
What makes Cisco DNA Center different from traditional network management applications and their management of networks?
A. It only supports auto-discovery of network elements in a green field deployment.
B. It modular design allows someone to implement different versions to meet the specific needs of an organization
C. IT abstracts policy from the actual device configuration
D. It does not support high availability of management functions when operating in cluster mode
Correct Answer: C
New Question
Which two actions are performed by the Weighted Random Early Detection mechanism? (Choose two)
A. It drops lower-priority packets before it drops higher-priority packets
B. It can identify different flows with a high level of granularity
C. It guarantees the delivery of high-priority packets
D. It can mitigate congestion by preventing the queue from filling up
E. IT supports protocol discovery
Correct Answer: AD
Explanation:
Weighted Random Early Detection (WRED) is just a congestion avoidance mechanism. WRED drops packets selectively based on IP precedence. Edge routers assign IP precedences to packets as they enter the network. When a packet arrives, the following events occur:
1. The average queue size is calculated.
2. If the average is less than the minimum queue threshold, the arriving packet is queued.
3. If the average is between the minimum queue threshold for that type of traffic and the maximum threshold for the interface, the packet is either dropped or queued, depending on the packet drop probability for that type of traffic.
4. If the average queue size is greater than the maximum threshold, the packet is dropped.
WRED reduces the chances of tail drop (when the queue is full, the packet is dropped) by selectively dropping packets when the output interface begins to show signs of congestion (thus it can mitigate congestion by preventing the queue from filling up). By dropping some packets early rather than waiting until the queue is full, WRED avoids dropping large numbers of packets at once and minimizes the chances of global synchronization. Thus, WRED allows the transmission line to be used fully at all times.
WRED generally drops packets selectively based on IP precedence. Packets with a higher IP precedence are less likely to be dropped than packets with a lower precedence. Thus, the higher the priority of a packet, the higher the probability that the packet will be delivered (-> answer A is correct).
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/qos_conavd/configuration/15-mt/qos-conavd-15-mt-book/qos-conavd-cfg-wred.html
Resources from:
1.2020 Latest Braindump2go 200-301 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/200-301.html
2.2020 Latest Braindump2go 200-301 PDF and 200-301 VCE Dumps Free Share:
https://drive.google.com/drive/folders/1N579lVwFMNcTo1QgOz_B6__zxBTx36ev?usp=sharing
3.2020 Latest Braindump2go 200-301 PDF and 200-301 VCE Dumps Free Share:
https://od.lk/fl/NDZfMTE3ODI2Nl8
Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!
 |
 |
 |
 |
 |
|
|---|---|---|---|---|---|
 |
 |
 |
 |
 |
|
| Braindump2go | Testking | Pass4sure | Actualtests | Others | |
| $99.99 | $124.99 | $125.99 | $189 | $29.99/$49.99 | |
| Up-to-Dated | ✔ | ✖ | ✖ | ✖ | ✖ |
| Real Questions | ✔ | ✖ | ✖ | ✖ | ✖ |
| Error Correction | ✔ | ✖ | ✖ | ✖ | ✖ |
| Printable PDF | ✔ | ✖ | ✖ | ✖ | ✖ |
| Premium VCE | ✔ | ✖ | ✖ | ✖ | ✖ |
| VCE Simulator | ✔ | ✖ | ✖ | ✖ | ✖ |
| One Time Purchase | ✔ | ✖ | ✖ | ✖ | ✖ |
| Instant Download | ✔ | ✖ | ✖ | ✖ | ✖ |
| Unlimited Install | ✔ | ✖ | ✖ | ✖ | ✖ |
| 100% Pass Guarantee | ✔ | ✖ | ✖ | ✖ | ✖ |
| 100% Money Back | ✔ | ✖ | ✖ | ✖ | ✖ |